Secure Text: Quick Overview Table
| Step | What You Do | Why It Matters | Tools/Methods |
|---|---|---|---|
| Step 1 | Classify your documents | Helps prioritize protection | Labels, access tiers |
| Step 2 | Encrypt files | Prevents unauthorized access | AES encryption, passwords |
| Step 3 | Control access | Limits exposure | Role-based permissions |
| Step 4 | Track usage | Detects suspicious behavior | Audit logs, analytics |
| Step 5 | Use secure platforms | Centralizes protection | Data Rooms, Virtual Data Rooms |
Introduction to Secure Text and Document Protection
In today’s digital-first business environment, protecting sensitive information is not optional—it is foundational. Whether you’re managing investor updates, legal contracts, or internal strategy documents, the concept of Secure Text plays a crucial role in maintaining confidentiality and trust.
Organizations involved in high-stakes activities like M&A deals or fundraising rely heavily on structured systems such as Data Rooms to ensure that their information remains protected throughout its lifecycle. Without proper safeguards, even a minor data leak can lead to financial losses or reputational damage.
Secure Text is not just about encryption—it is about creating a complete ecosystem where documents are controlled, monitored, and shared with precision. This blog walks through practical steps to achieve that level of protection.
Why Secure Text Matters More Than Ever
Data breaches are no longer rare events—they are frequent and increasingly sophisticated. Businesses handling confidential documents need a system that ensures Secure Text is maintained across every interaction, from upload to sharing and viewing.
When companies use Virtual Data Rooms for due diligence or investor communication, they are not just storing files—they are enabling controlled collaboration. Without structured safeguards, sensitive files can be copied, downloaded, or shared without permission.
The growing importance of compliance regulations also makes it essential to adopt secure systems. Whether it’s financial audits or legal reviews, maintaining Secure Text ensures that your organization stays compliant and credible.
Step 1: Classify Your Documents Properly
The first step in protecting any document is understanding its sensitivity. Not all files require the same level of security, and applying uniform protection can either be inefficient or insufficient.
By categorizing documents into levels such as public, internal, confidential, and highly sensitive, you create a structured approach to Secure Text. This classification helps determine who can access what and under what conditions.
For example, in M&A processes, financial statements and legal agreements should always be treated as highly sensitive. Using Data Rooms allows you to assign these classifications and enforce them consistently across teams.
Step 2: Encrypt Files to Ensure Secure Text
Encryption is the backbone of document security. Without encryption, files are vulnerable to interception and unauthorized access, especially when shared over the internet.
Modern encryption standards like AES-256 ensure that even if a file is intercepted, it cannot be read without the proper key. This is a critical component of maintaining Secure Text in any organization handling sensitive data.
Platforms like DeelTrix integrate encryption directly into their systems, ensuring that files remain protected both at rest and in transit. This eliminates the need for manual encryption processes and reduces human error.
Step 3: Implement Strong Access Controls
Access control is where most organizations either succeed or fail in maintaining Secure Text. Simply encrypting a document is not enough if too many people have access to it.
Role-based permissions allow you to define exactly who can view, edit, download, or share a document. This ensures that only authorized individuals can interact with sensitive files.
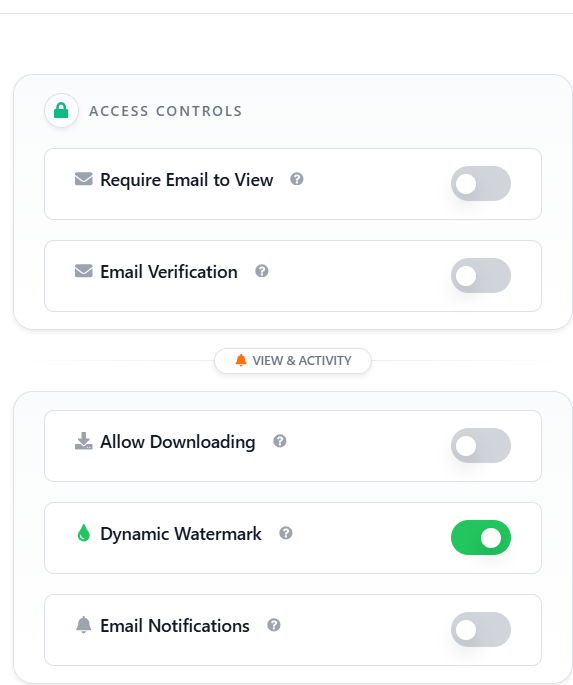
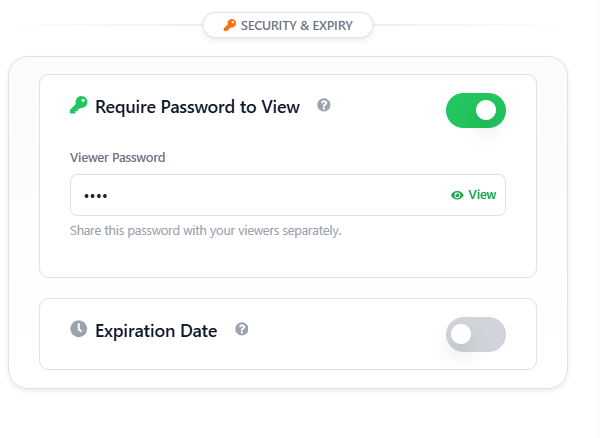
In Virtual Data Rooms, you can go even further by setting time-based access, restricting downloads, and preventing screenshots. These features are especially useful in M&A transactions where multiple stakeholders need controlled access.
Step 4: Use Dynamic Watermark for Accountability
One of the most effective ways to deter unauthorized sharing is by using Dynamic Watermark technology. This feature overlays user-specific information such as email ID, timestamp, or IP address directly onto the document.
When users know that their identity is embedded in the file, they are far less likely to misuse it. This creates a psychological and technical layer of protection that strengthens Secure Text practices.
Dynamic Watermark is widely used in Data Rooms to ensure accountability during sensitive processes like due diligence. It not only protects documents but also provides traceability in case of leaks.
Step 5: Monitor Document Activity in Real-Time
Tracking how documents are used is essential for maintaining Secure Text. Without visibility, you cannot detect suspicious behavior or respond to potential threats.
Advanced analytics tools in Virtual Data Rooms allow you to monitor who accessed a file, how long they viewed it, and what actions they performed. This level of insight is invaluable for identifying unusual patterns.
For instance, if a user suddenly downloads multiple sensitive files in a short period, the system can flag this activity. This proactive approach ensures that risks are identified and mitigated early.
Step 6: Choose Secure Platforms Like DeelTrix
The platform you choose plays a critical role in how effectively you can implement Secure Text. Generic file-sharing tools often lack the advanced security features required for sensitive business operations.
Specialized platforms like DeelTrix are designed specifically for secure document sharing. They combine encryption, access control, activity tracking, and compliance features into a single system.
By using such platforms, organizations can streamline their workflows while ensuring that their data remains protected at all times. This is particularly important for industries dealing with M&A, legal documentation, and investor relations.
Role of Data Rooms in Secure Document Sharing
Data Rooms have become the standard for secure document management in high-stakes environments. They provide a centralized space where documents can be stored, shared, and monitored with complete control.
Unlike traditional storage systems, Data Rooms are built with security as a core feature. They support Secure Text through encryption, access control, and detailed audit logs.
In M&A transactions, Data Rooms enable seamless collaboration between buyers, sellers, and advisors while ensuring that sensitive information is never exposed unnecessarily.
How Virtual Data Rooms Enhance Security
Virtual Data Rooms take document security to the next level by offering advanced features tailored for modern business needs. They eliminate the risks associated with physical storage and manual sharing methods.
With Virtual Data Rooms, organizations can enforce Secure Text policies across all documents. Features like restricted viewing, watermarking, and activity tracking ensure that every interaction is secure.
These platforms are particularly useful for remote teams and global transactions, where secure access to documents is required across different locations.
Common Mistakes That Break Secure Text
Many organizations unknowingly compromise their document security due to poor practices. One common mistake is sharing sensitive files over email without proper encryption or access control.
Another issue is failing to revoke access after a project is completed. This leaves documents exposed to individuals who no longer need them, weakening Secure Text measures.
Using unsecured storage systems or outdated tools can also create vulnerabilities. To avoid these risks, it is essential to adopt modern solutions like Virtual Data Rooms and follow best practices consistently.
Secure Text in M&A Transactions
M&A deals involve the exchange of highly sensitive information, including financial data, intellectual property, and legal agreements. Maintaining Secure Text in such scenarios is critical to the success of the transaction.
Data Rooms provide a secure environment where all stakeholders can access necessary documents without compromising confidentiality. They also ensure that every action is logged and traceable.
By using advanced tools like Dynamic Watermark and access controls, organizations can protect their data throughout the entire M&A lifecycle.
Future of Secure Document Management
As technology evolves, so do the methods used to protect documents. Artificial intelligence and machine learning are being integrated into Virtual Data Rooms to enhance Secure Text capabilities.
These technologies can analyze user behavior, detect anomalies, and automatically enforce security policies. This reduces the reliance on manual monitoring and improves overall efficiency.
The future of document security lies in automation and intelligent systems that can adapt to emerging threats while maintaining seamless user experiences.
Conclusion
Protecting documents is no longer just a technical requirement—it is a strategic necessity. By following the steps outlined in this guide, organizations can ensure that their data remains secure at all times.
From classification and encryption to access control and monitoring, each step contributes to maintaining Secure Text across the document lifecycle.
Using advanced platforms like DeelTrix and leveraging tools such as Dynamic Watermark and Virtual Data Rooms can significantly enhance your security posture, especially in complex processes like M&A.
FAQ’s
What is Secure Text in document management?
Secure Text refers to the methods and technologies used to protect sensitive information within documents from unauthorized access or misuse. It includes encryption, access control, and monitoring.
How do Virtual Data Rooms improve document security?
Virtual Data Rooms provide centralized, secure environments with features like encryption, access control, and activity tracking, ensuring complete protection of sensitive files.
Why is Dynamic Watermark important?
Dynamic Watermark adds user-specific information to documents, discouraging unauthorized sharing and enabling traceability in case of data leaks.
Is DeelTrix secure for sensitive document sharing?
Yes. DeelTrix is ISO Certified and ensure data residency by allowing user select their data room location for file storage.
What industries benefit most from Secure Text practices?
Industries like finance, legal, healthcare, and technology benefit significantly, especially during processes like M&A where data confidentiality is critical.


